A number of devices are running Linux due to its flexibility and open source nature. This has made Linux platform the target for malware attacks, so it becomes important to analyze the Linux malwares. Today, there is a need to analyze Linux malwares in an automated way to understand its capabilities.
Limon is a sandbox developed as a research project written in python, which automatically collects, analyzes, and reports on the run time indicators of Linux malware. It allows one to inspect the Linux malware before execution, during execution, and after execution (post-mortem analysis) by performing static, dynamic and memory analysis using open source tools. Limon analyzes the malware in a controlled environment, monitors its activities and its child processes to determine the nature and purpose of the malware. It determines the malware’s process activity, interaction with the file system, network, it also performs memory analysis and stores the analyzed artifacts for later analysis. Since Limon relies on open source tools, it’s easy for any security analyst to setup a personal sandbox to perform Linux malware analysis. This blog post will touch on details of Linux malware analysis,features and setting up of Limon sandbox.
Link to Download Limon: Limon Linux Sandbox
Setting Up and Configuring Limon: Setting up Limon for Analyzing Linux Malwares
Link to Black Hat Europe 2015 presentation: Automating Linux Malware Analysis Using Limon Sandbox
Why Malware Analysis?
Malware is a piece of software which causes harm to a computer system without the owner’s consent. Viruses, Trojans, worms, backdoors, rootkits and spyware can all be considered as malwares.
With new malware attacks making news every day and compromising company’s network and critical infrastructures around the world, malware analysis is critical for anyone who responds to such incidents.
Malware analysis is the process of understanding the behaviour and characteristics of malware, how to detect and eliminate it.
There are many reasons why we would want to analyze a malware, below to name just a few:
- Determine the nature and purpose of the malware i.e. whether the malware is an information stealing malware, http bot, spam bot, rootkit, keylogger, RAT etc.
- Interaction with the Operating System i.e. to understand the file system, process and network activities.
- Detect identifiable patterns (network and host based indicators) to cure and prevent future infections
Types of Malware Analysis
In order to understand the characteristics of the malware three types of analysis can be performed they are:
- Static Analysis
- Dynamic Analysis
- Memory Analysis
In most cases static and dynamic analysis will yield sufficient results however Memory analysis gives post-mortem perspective and helps in determining hidden artifacts, rootkit and stealth malware capabilities.
Static Analysis
Static Analysis involves analyzing the malware without actually executing it. Following are the steps:
- Determining the File Type: Determining the file type can also help you understand the type of environment the malware is targeted towards, for example if the file type is ELF (Executable and Linkable format) format which is a standard binary file format for Unix and Unix-like systems, then it can be concluded that the malware is targeted towards a Unix or Unix flavoured systems
- Determining the Cryptographic Hash: Cryptographic Hash values like MD5 and SHA1 can serve as a unique identifier for the file throughout the course of analysis. Malware, after executing can copy itself to a different location or drop another piece of malware, cryptographic hash can help you determine whether the newly copied/dropped sample is same as the original sample or a different one. With this information we can determine if malware analysis needs to be performed on a single sample or multiple samples. Cryptographic hash can also be submitted to online antivirus scanners like VirusTotal to determine if it has been previously detected by any of the AV vendors. Cryptographic hash can also be used to search for the specific malware sample on the internet.
- Strings search: Strings are plain text ASCII and UNICODE characters embedded within a file. Strings search give clues about the functionality and commands associated with a malicious file. Although strings do not provide complete picture of the function and capability of a file, they can yield information like file names, URL, domain names, ip address, attack commands etc.
- File obfuscation (packers, cryptors) detection: Malware authors often use softwares like packers and cryptors to obfuscate the contents of the file in order to evade detection from anti-virus softwares and intrustion detection systems. This technique slows down the malware analysts from reverse engineering the code.
- Determine Fuzzy Hash: Comparing the malware samples collected or maintained in a private or public repository is an important part of file identification process. The easiest way to check for file similarity is through a process called “Fuzzy Hashing”. Fuzzy hash comparison can tell the percentage similarity between the files. Fuzzy hash comparison is a method by which identical files can be identified. This can help in determine the variants of the same malware.
- Submission to online Antivirus scanning services: This will help you determine if the malicious code signatures exist for the suspect file. The signature name for the specific file provides an excellent way to gain additional information about the file and capabilities. By visiting the respective antivirus vendor web sites or searching for the signature in search engines can yield additional details about the suspect file. Such information may help in further investigation and reduce the analysis time of the malware specimen. VirusTotal (http://www.virustotal.com) is a popular web based malware scanning services.
- Inspecting File Dependencies: Executable loads multiple shared libraries and call api functions to perform certain actions like resolving domain names, establishing an http connection etc. Determining the type of shared library and list of api calls imported by an executable can give an idea on the functionality of the malware.
- Examining ELF File Structure: ELF stands for “Executable and Linkable Format” this is a standard binary file format for Linux systems. Examining the ELF file structure can yield wealth of the information including Sections, Symbols and other file metadata information.
- Disassembling the File: Examining the suspect program in a disassembler allows the investigator to explore the instructions that will be executed by the malware. Disassembly can help in tracing the paths that are not usually determined during dynamic analysis.
Dynamic Analysis
Dynamic Analysis involves executing the malware sample in a controlled environment and monitoring as it runs. Sometimes static analysis will not reveal much information due to obfuscation, packing in such cases dynamic analysis is the best way to identify malware functionality. Following are some of the steps involved in dynamic analysis:
- Monitoring Process Activity: This involves executing the malicious program and examining the properties of the resulting process and other processes running on the infected system. This technique can reveal information about the process like process name, process id, child processes created, system path of the executable program, modules loaded by the suspect program.
- Monitoring File System Activity: This involves examining the real time file system activity while the malware is running; this technique reveals information about the opened files, newly created files and deleted files as a result of executing the malware sample.
- Monitoring Network Activity: In addition to monitoring the activity on the infected host system, monitoring the network traffic to and from the system during the course of running the malware sample is also important. This helps to identify the network capabilities of the specimen and will also allow us to determine the network based indicator which can then be used to create signatures on security devices like Intrusion Detection System
- System Call Tracing: System calls made by malware can provide insight into the nature and purpose of the executed program such as file, network and memory access. Monitoring the system calls can help determine the interaction of the malware with the operating system.
Memory Analysis
Memory Analysis also referred to as Memory Forensics is the analysis of the memory image taken from the running computer. Analyzing the memory after executing the malware sample provides post-mortem perspective and helps in extracting forensics artifacts from a computer’s memory like:
- running processes
- network connections
- shared libraries
- loaded kernel modules
- code injections
- Rootkit capabilities.
- API Hooking
Limon Linux Sandbox
Limon is a sandbox for automating Linux malware analysis. It was developed as a research project for learning Linux malware analysis. It is written in python and uses custom python scripts and various open source tools to perform static, dynamic/behavioural and memory analysis.
Limon Linux Sandbox: Download
Working of Limon
Limon performs below steps for analyzing the linux malware samples.
- Takes sample as input
- Performs static analysis
- Starts the Virtual Machine(VM)
- Transfers the malware to VM
- Runs the monitoring tools ( to monitor process, file system, network activity etc)
- Executes the malware for the specified time
- Stops the monitoring tools
- Suspends the VM
- Acquires the memory image
- Performs memory analysis using Volatility framework
- Stores the results (Final reports, destkop screenshot, pcaps and malicious artifacts for later analysis)
Tools Used by Limon
Limon relies on below tools to perform static, dynamic and memory analysis
- Custom python scripts
- YARA-python (https://github.com/plusvic/yara)
- VirusTotal Public api (https://www.virustotal.com/en/documentation/public-api/)
- ssdeep (http://ssdeep.sourceforge.net/)
- strings utility (http://linux.die.net/man/1/strings)
- ldd (http://linux.die.net/man/1/ldd)
- readelf (https://sourceware.org/binutils/docs/binutils/readelf.html)
- Inetsim (http://www.inetsim.org/downloads.html)
- Tcpdump (http://www.tcpdump.org/)
- strace (http://linux.die.net/man/1/strace)
- Sysdig (http://www.sysdig.org)
- Volatility memory forensics framework (http://www.volatilityfoundation.org/#!releases/component_7140)
Supported File Types
Limon can analyze below file types (both with and without parameters) :
- ELF Executable(both x86 and x86_64)
- Perl Script
- Python script
- Shell script
- Bash script
- PHP script
- Loadable kernel module(LKM)
Setting Up and Configuring Limon
For Limon to work, proper setup of the environment is required (this is a one-time setup).Please refer the below Link for setting up and configuring Limon.
http://malware-unplugged.blogspot.com/2015/11/setting-up-limon-sandbox-for-analyzing.html
General Features of Limon
- Option to run in sandbox mode (does not allow to connect to c2)
- Option to run in internet mode (connects to c2)
- Simulates all services (like dns, http and other protocols) when run in sandbox mode
- Option to run malware for specified time (default is 60 seconds)
- Captures desktop screenshot
- Reports on the malware behaviour
Static Analysis Features
Below are the static analysis capabilities of Limon:
- Determines File Type
- Determines File Size
- Determines md5 hash
- Determines fuzzy hash(ssdeep hash)
- Comparison of fuzzy hash with previously submitted samples to determine similar variants
- Display ELF header Structure
- Dumps ASCII and UNICODE strings
- Determines packers using YARA rules
- Determines malware capability using YARA rules (ability to run custom YARA rules will be added soon)
- Perfoms md5 search on VirusTotal(does not submit samples)
- Displays dependencies of the malware (shared objects)
- Displays program header structures
- Displays section header information
- Displays symbol table (both static and dynamic symbols)
Dynamic Analysis Features
Limon gives different options for performing dynamic analysis to track activity of the malware(during execution), below are the different options:
- Filtered call trace for tracing system calls related to file, process, network activity
- Unfiltered call trace – traces all system calls (more noisy)
- Filtered system event montioring to track file, process, network activity (less noisy)
- Unfiltered system even monitoring to track file, process, network, memory allocations/unallocations, signals etc (more noisy)
- Shows DNS summary
- Shows TCP conversations
- Stores packet captures
- Stores event trace dump
Memory Analysis features
Limon performs post-mortem analysis by performing memory analysis using Volatility framework. This feature should help in detecting stealthy rootkits and malwares performing Anti-Forensic tricks. Below are the memory analysis features:
- Option to perform verbose memory forensics (slow)
- Process Listing (using different methods)
- Process tree listing
- Process listing with process arguments
- Displays thread associated with each process
- Dispays Network connections (TCP and UDP)
- Displays Interface Information
- Displays processes running with RAW sockets
- Displays shared libaries associated with the processes (using different methods)
- Displays kernel modules
- Dislays kernel modules hidden from module list but present in SYSFS
- Displays Kernel modules hidden from both module list and SYSFS
- Displays files opened within kernel
- Displays processes sharing credential structures
- Checks for keyboard notifier hooks
- Checks for TTY hooks
- Checks for system call table modification
- Displays BASH history
- Checks for modified file operation structures
- Checks hooked network operation function structures
- Checks netfilter hooks
- Check inline kernel hooks
- Checks for code or binary injection
- Check for PLT/GOT hooks (only in verbose mode)
- Checks for userland api hooks (only in verbose mode)
Analysis of Linux Malware Tsunami using Limon
Video Demo of Analysis of Tsunami using Limon:
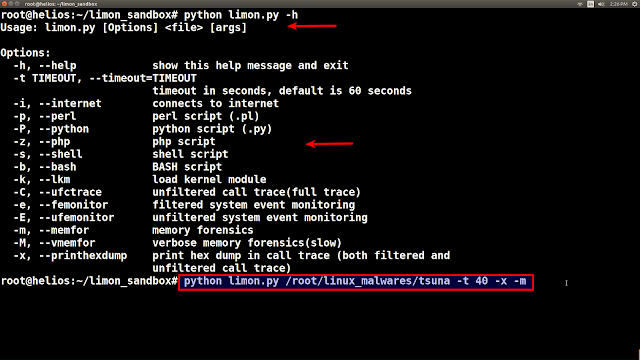
To demonstrate the working of Limon, Linux malware sample “Tsunami” was run in Limon for 40 seconds as shown in the screenshot below. This section contains the analysis details of the Linux malware “Tsunami”. The screenshots also shows different options in Limon.
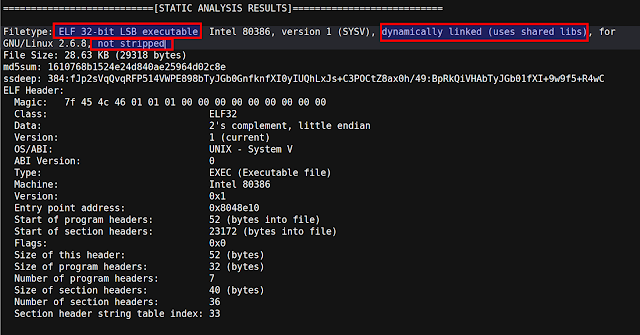
Below screenshot shows some of the static analysis results after analyzing the malware in Limon. The malware is 32 bit ELF executable, its dynamically linked and the symbols are not stripped. Below screenshot also shows md5, ssdeep(fuzzy) hash and ELF metadata
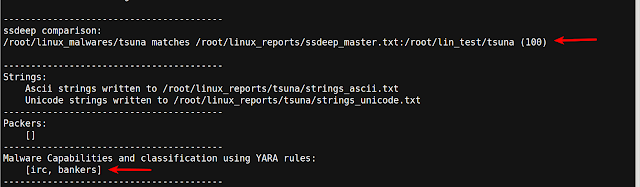
When a malware is submitted to Limon, Limon determines the ssdeep hash (fuzzy hash) and compares the fuzzy hash with the master list of fuzzy hashes of previously submitted samples. In this case the malware fuzzy hash has 100% match with the previously submitted sample, indicating that it is the same malware sample and the malware sample was also run against YARA rules to determine malware capabilities. As shown in the below screenshot it looks like malware has IRC capabilities.
When the malware is submitted to Limon, it determines the md5 hash of the sample and uses the md5sum to search the VirusTotal using its public api. In this case the sample is detected by AV vendors as Tsunami.

Symbol information shows references to network related system calls indicating the network capability of the malware.

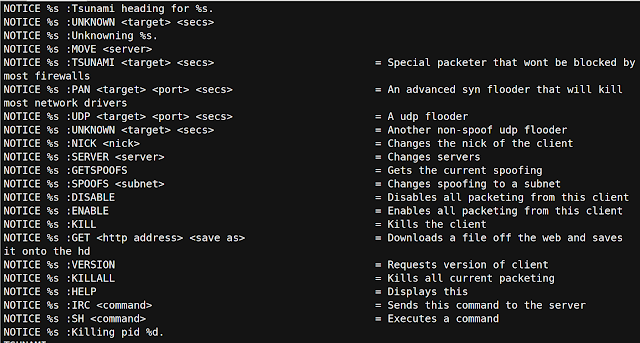
Strings from the malware sample shows references to the C2 ip and references to http and IRC commands
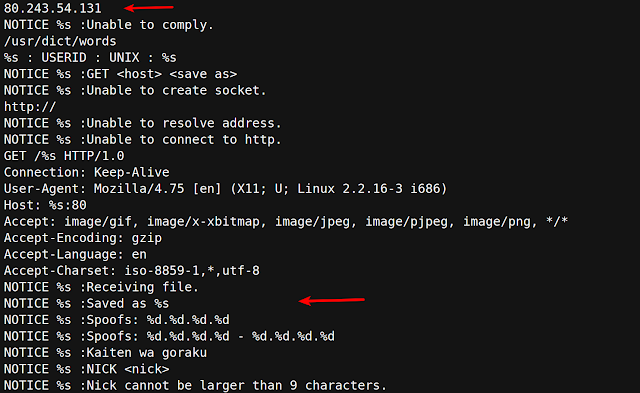
Strings extracted from the malware also shows the references to the attacks commands of the malware, from the strings it looks like the malware has DOS/DDOS capabilities.
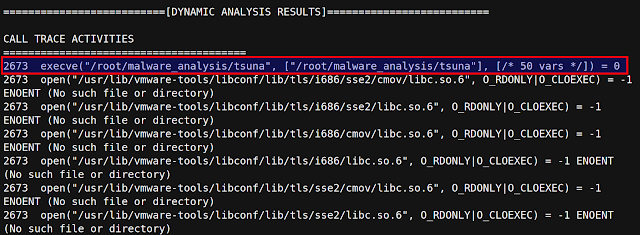
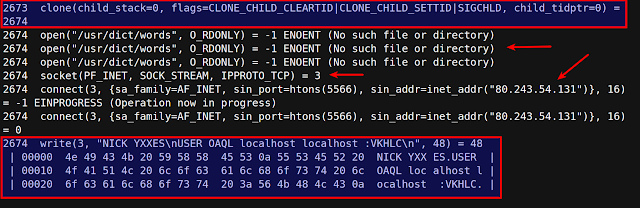
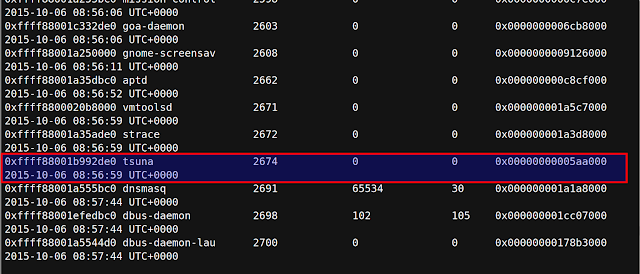
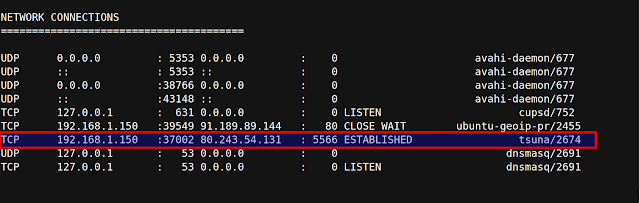
The screenshots below shows the dynamic analysis results. The malware was successfully executed by Limon, after execution the malware creates a child process (with pid 2674). The child process tries to read a file /usr/dict/words which does not exist. From the name of the file it looks like it’s a dictionary file which malware uses for some kind of password cracking. Also the malware creates a network socket, establishes a connection with the C2 ip on port 5566 and writes some content on the socket.
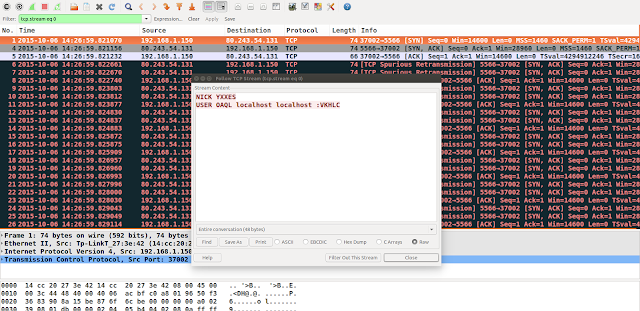
The packet capture shows the IRC communication made by the malware to the C2 ip on port 5566. The malware is an IRC bot
Process listing from the memory analysis results shows the malicious process “tsuna” running with a pid 2674
Network connections from the memory analysis shows that the process “tsuna” (with pid 2674) established the connection to the C2 ip on port 5566
Conclusion
Linux is growing in its popularity and with multiple devices running Linux it has become target for malware attacks, so it becomes important to analyze the Linux malware in an automated way to determine the network and host based indicators. This blog provided a high level introduction to malware analysis and also introduced a tool “Limon” to perform static, dynamic and memory analysis of Linux malwares. The blog post also covered setting up of Limon and analysis of a Linux malware called “tsunami” using Limon, which helped in determining the various capabilities of the malware.
Link to Download Limon: Limon Linux Sandbox
Setting Up and Configuring Limon: Setting up Limon for Analyzing Linux Malwares
Link to Black Hat Europe 2015 presentation: Automating Linux Malware Analysis Using Limon Sandbox