On Nov 10, 2013 FireEye published a blog about how the latest IE zero day exploit was used in the wild by the APT actors to serve 9002 RAT (aka Hydraq/McRat/Mdmbot). The FireEye blog also mentioned that the threat actors directly injected the payload of 9002 RAT into memory without writing to disk. This technique was used to bypass the traditional forensic method. more details can be found here Operation Ephemeral Hydra
I wanted to figure out a quick method of detecting APT RAT 9002 (both disk and diskless method)
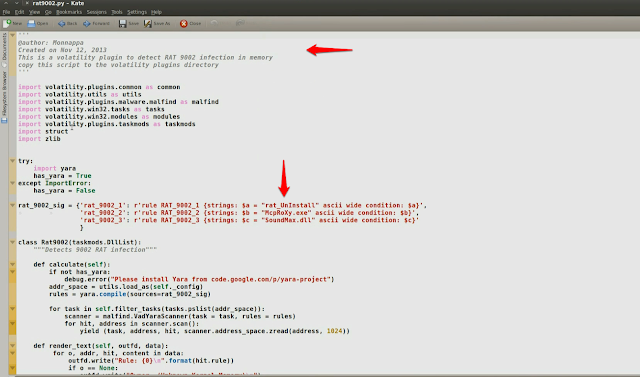
infection. In order to do that i analyzed few samples of the 9002 RAT and also based on some of the information mentioned in the FireEye blog, I wrote a Volatility plugin to detect RAT 9002 infection in Memory.
Preparation
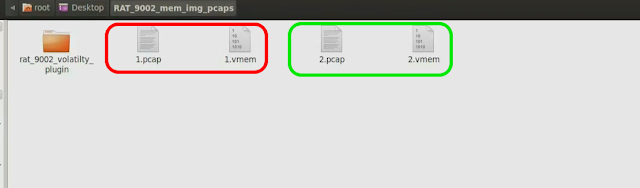
I analyzed few 9002 RAT samples (104130d666ab3f640255140007f0b12d and acbc249061a6a2fb09271a68d53567d9) in the sandbox and collected the pcaps and the memory images. Below screenshot shows the pcaps and the memory images collected after running the samples in the sandbox. The one shown in the red is the pcap and memory image after running the first RAT 9002 sample and the one in green is the pcap and memory image collected after running the second sample
Video Demo related to this blog post can be viewed below:
https://www.youtube.com/watch?v=JTtgXZTstJU
a) Investigating the first sample (1.pcap and 1.vmem)
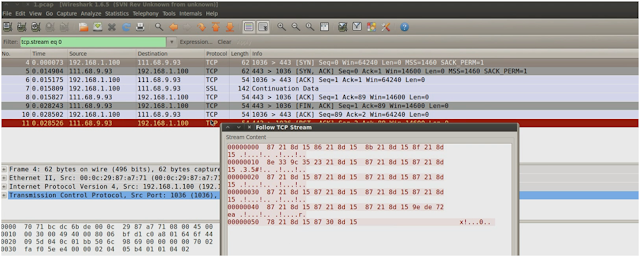
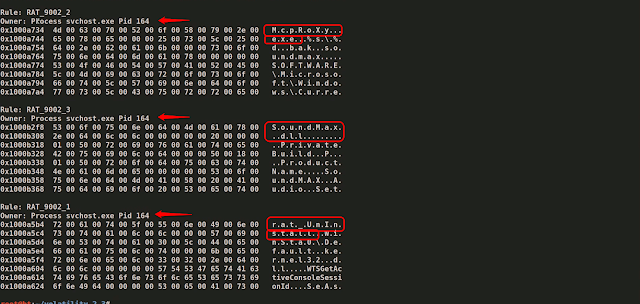
Below screenshot shows the RAT 9002 communication, as you can see malware is talking to the cnc ip “111.68.9.93” on port 443
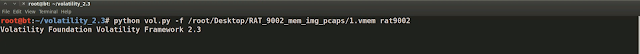
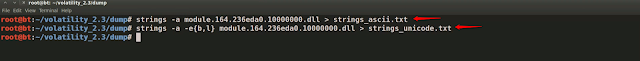
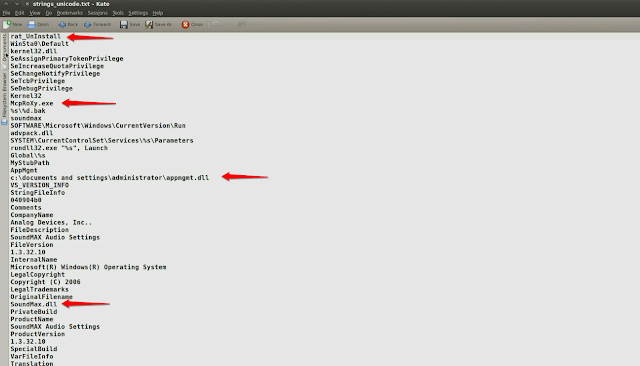
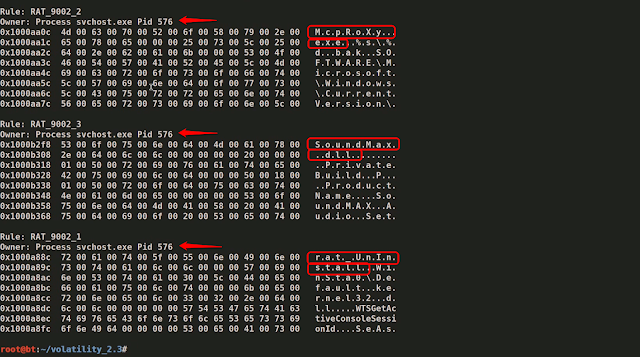
In order to automatically determine the RAT 9002 infection in the memory, I wrote a Volatility plugin (rat9002.py) which narrows down on the malicious process by searching for the RAT 9002 artifacts in memory. Below screenshot shows the volatility plugin and the indicators (rat_UnInstall, McpRoXy.exe and SoundMax.dll) that are present in the variants of RAT 9002 (as mentioned in the FireEye blog) which can be used to determine the infection in memory.
Volatility plugin can be downloaded from GitHub
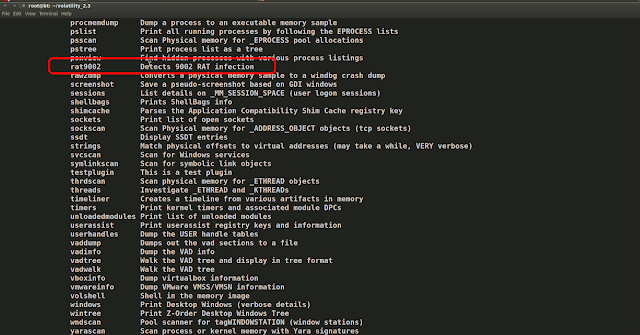
after copying this script to the Volatility plugins directory, Volatility detected the plugin as shown below
after running the plugin against the memory image (1.vmem), it detected the indicators that i was looking for, these indicators were detected in the address space of svchost.exe process (with pid 164). With the help of the plugin i was able to narrow down on the malicious process (pid 164)
Running the connscan module also confirms that the malicious communication to the ip 111.68.9.93 on port 443 that we saw in the pcap is associated with svchost.exe (with pid 164)
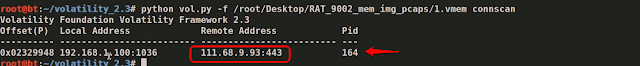
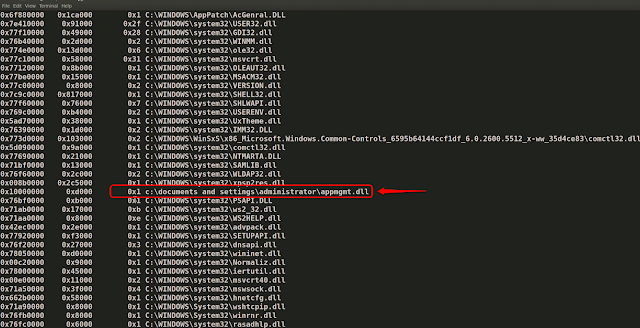
Now svchost.exe (with pid 164) is our suspicious process, but since svchost.exe is the legitimate OS process, and also the functionality of svchost.exe is to load DLL’s running as service, there is a possibility that svchost.exe loaded a malicious DLL, In order to identify malicious DLL i ran dlllist plugin. Below screenshot shows the DLL loaded by the svchost.exe (pid 164), also you can see a suspicious dll loaded from a non standard path.
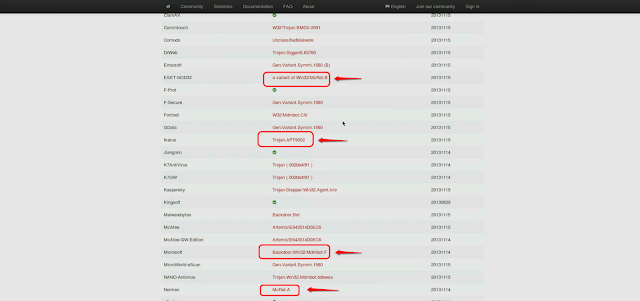
after dumping this DLL (appmgmt.dll) from memory and submitting to VirusTotal, AntiVirus vendors detect this as (McRat/Mdmbot) which is same as RAT 9002
ASCII and Unicode strings from the dumped DLL shows the presence of the RAT 9002 indicators (rat_UnInstall, McpRoXy.exe and SoundMax.dll). This further confirms that the dumped DLL is component of RAT 9002
b) Investigating the second sample(2.pcap and 2.vmem)
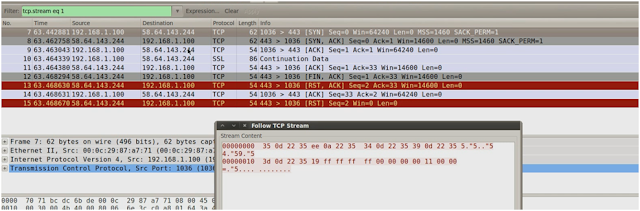
Below screenshot shows the RAT 9002 communication from the second sample. In this case malware is talking to the cnc ip “58.64.143.244” on port 443
After running the rat9002 plugin on the memory image of the second sample (2.vmem), the plugin detected the malicious process as svchost.exe (with pid 576)
The below screenshot confirms that the malicious communication was made by the pid 576 (as detected by the plugin).
svchost.exe (pid 576) can be further inspected (similar to the first sample) for any malicious artifacts.
Both the samples that i analyzed were traditional 9002 RAT (not the diskless version of RAT), but this technique will work for diskless (in memory) version of RAT 9002 as well. As per the FireEye blog, the diskless RAT contains the string “rat_UnInstall” and since my plugin is looking for that indicator it will still be able to find the malicious process (or the process which contains malicious code).
With a powerful memory forensics tool like Volatility, even if the malware hides its presence on the disk, we can still determine its presence in the memory.