In late December a cyber attack caused power outage for few hours in the Ivano-Frankivsk region in Ukraine as mentioned here. Threat researchers from ESET linked this attack to a malware called “BlackEnergy” which attacked electricity distribution companies in Ukraine. This blog post contains the memory analysis details of BlackEnergy big dropper (SHA-1:896FCACFF6310BBE5335677E99E4C3D370F73D96) mentioned in the ESET blog
This post also covers the details of the user mode and kernel mode components of BlackEnergy Rootkit and also covers some of the stealth techniques of BlackEnergy Rootkit.
Sandbox Analysis
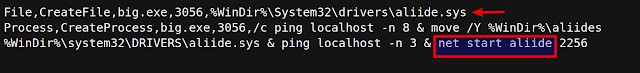
The analysis started by running the malware sample in the sandbox. Running the BlackEnergy 3 big dropper created a file aliide.sys in system32\drivers directory. On a clean system the driver with same name (aliide.sys) exists, which is the Ali mini IDE driver from Acer Laboratories. After executing the BlackEnergy dropper, it replaces the clean driver and then loads the malicious driver by starting it as service using “net start aliide” as shown below.
Comparing the clean and BlackEnergy infected memory image
Examining the service information on a clean system (not infected with BlackEnergy) shows that legitimate aliide service is set to on demand start (service need to be manually started) and the service is in the stopped state. as shown below
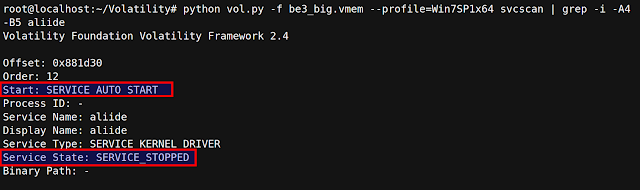
Examining the service information of the memory image after executing BlackEnergy3 dropper shows that, apart from replacing the aliide driver (aliide.sys) on the disk, the aliide service is set to auto start (service starts automatically when system starts) and also the service is still in the stopped state, this means after restarting the system, the service will automatically start and load the malicious aliide.sys driver.
Comparing the clean and malicious aliide.sys
Before restarting the system, aliide.sys from the clean and infected machine was collected and compared, After comparison many differences in the files were spotted, indicating that the original aliide.sys was replaced with malicious aliide.sys
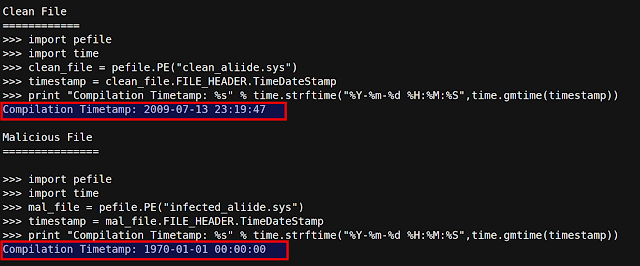
Below screenshot shows the discrepancy in the compilation timestamp between the two files, notice how the compilation timestamp of malicious driver (aliide.sys) is set to 1970
Below screenshot shows the discrepancy in file description, file size and the original filename. On the left hand side is the file details of clean aliide.sys. On the right hand side is the file details of the malicious driveraliide.sys dropped by BlackEnergy
Below screenshot shows the discrepancy in the digitial certificates. BlackEnergy used fake digital certificates (on the right hand side) and also notice how the expiration date of the certificate is set to 2040. The use of fake certificates by BlackEnergy is also mentioned in the Mcafee blog
Analysis after restarting the infected system
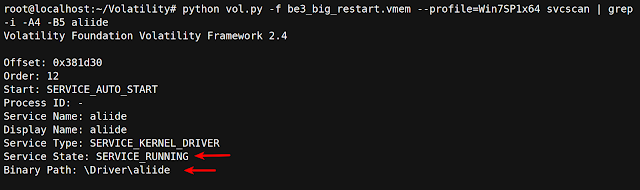
To determine the behavior of the malware the system was restarted so that the service (aliide) can start and the driver gets loaded, as you can see after restarting the system, the service was started with service name“aliide”
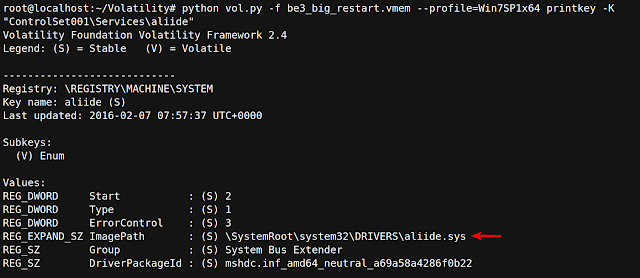
Querying the service registry key shows that the driver associated with the service is aliide.sys (which is the malicious driver which replaced the actual aliide.sys). This shows how BlackEnergy performs disk based service Hijack to persist on the system. This is hard to detect because there is no difference in the path to the driver but on the disk the file has been replaced with the malicious driver.
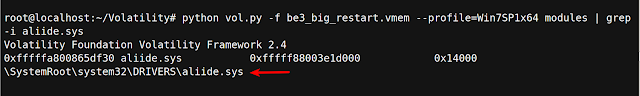
Below screenshot confirms that the malicious driver was loaded as a result of starting the service.
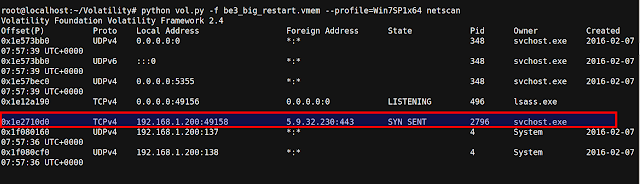
Once the driver was loaded, malicious network connection to the ip address 5.9.32.230 was detected on port 443. This is one of the BlackEnergy3 C2 ip as mentioned in the Mcafee blog
Looking at the network connection shows that the connection to the c2 ip address 5.9.32.230 was made by the process svchost.exe with pid 2796
Searching for the C2 ip address using yarascan also found the C2 ip in the address space of svchost.exe (pid 2796), the pattern matches with the BlackEnergy network communication pattern mentioned in the Kaspersky blog
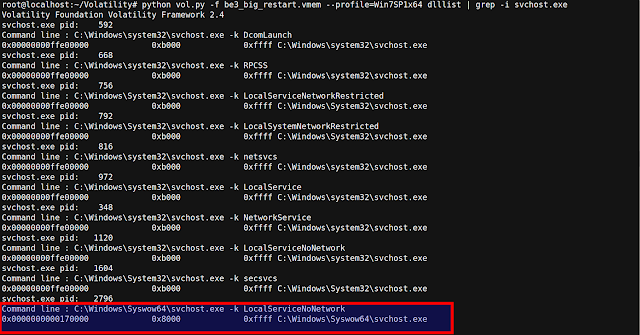
Comparing the svchost.exe (pid 2796) with other svchost.exe processes that run on the system, shows that svchost.exe with pid 2796 is running from Syswow64 directory instead of system32 directory
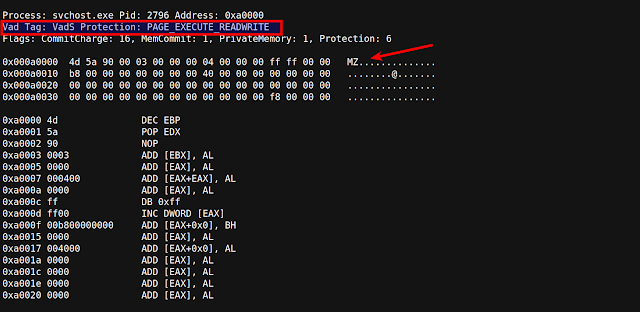
Below screenshot shows presence of PE file in the address space of svchost.exe (pid 2796), also the memory permissions and the VAD structure used (short VAD) confirms that PE file was injected into svchost.exe. As a result of injecting PE file, svchost.exe (pid 2796) performed malicious activity (like contacting the C2 ip)
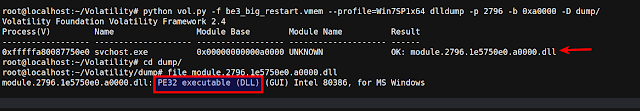
Dumping the injected PE file confirms the file to be DLL. In this case once the malicious driver was loaded by the aliide service, the driver injected dll into the svchost.exe (pid 2796)
VirusTotal Results for the dumped DLL confirms it to be component of BlackEnergy Rootkit
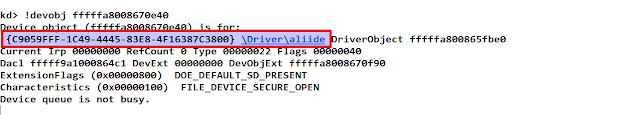
In order to interact with the user mode code component (DLL), The malicious driver (aliide.sys) creates a device {C9059FFF-1C49-4445-83E8-4F16387C3800}
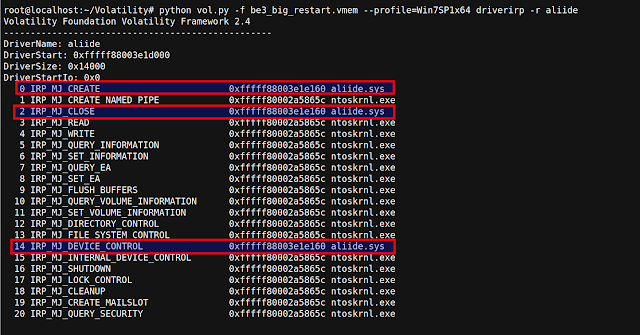
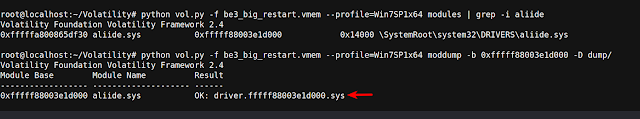
The below screenshot shows dispatch routines set by the driver giving an idea of IRPs handled by the driver.
Dumping the driver and opening it in IDA shows references to the device and the symbolic name of the device
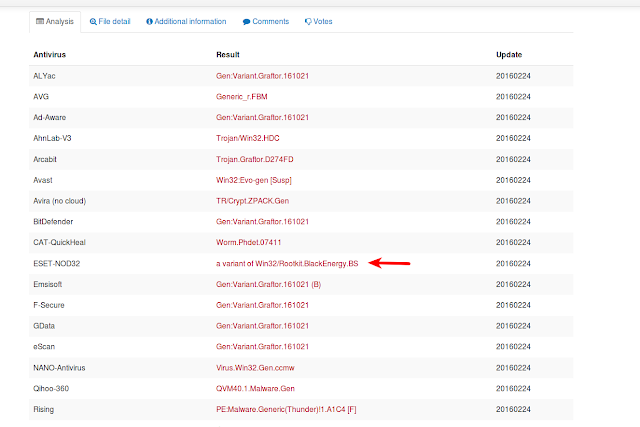
VirusTotal results for the dumped driver show very less detections but some AV vendors confirm it as Black Energy Rookit
Conclusion
BlackEnergy Rootkit remains stealthy by replacing the existing driver on the disk, even though this kind of technique is difficult to detect using memory forensics but by comparing memory artifacts on the clean system with the memory artifacts on the infected machine (like the service information) can help in detecting the BlackEnergy Rookit. Also comparing file details (compilation timestamp, file size, digital certificates) of driver files on the clean and infected system can give an indication of the malicious activity. Since the driver injects DLL into the svchost.exe this technique can very well be detected using memory forensics because of the obvious artifacts created in the memory.







Good Analysis. Thanks for Sharing