Hello there! before we begin our journey, spare some time to update the below spyware signature (No detections anywhere) in all your controls, which digests IOCs:
MD5 – 68AB498574C0BEAE225A04D04A2571A1 (new variant of spyware)
NB:
- The day was sunny and was analyzing a targeted spam mail and its attached macro malware – normal routine 🙂
- But this investigation , lead me to a brand new variant of spyware which has no detection as of this writing.
- This whole article circles around phishing, macro malware, its command and control, creeping into command and control and then finding another brand new spyware which is yet to get kick started by hacker.
- I am sure this campaign is already started 😉
- The article consists two areas of focus : one normal macro malware analysis and the second is the investigation against a malware within the Command and Control server.
- I maximum tried to keep this article less technical, but ya, some areas it is inevitable.
Ok now let’s start…
Part 1 🙂
One spam mail was spreading in a Government firm in which specializes in Renewable energy and concept of clean energy.

The mail came from a remote IP address which belongs to Etisalat Nigeria:

The spam mail had an attachment “ORDER_#1403.xls” and the sender was found to be spoofed. Now, how I confirmed that it was spoofed? , the mail header didn’t give much artifacts that it is spoofed, well, some points really points the finger that it is spoofed.
When we closely look at the sender ‘satis@pemenerji.com.tr’ belongs to a turkey based proactive energy management company which is one of the distribution partner of Huawei solar technology wing from Turkey.

“Satis” in Turkish is “sales”, so the mail claims to be originated from sales mail ID of pemenerji firm.
This e-mail ID might have harvested from internet, one example is, the same e-mail ID was revealed in recent Huawei notification of seminar conducted by pemerji:

Also the mail signature and address of the Pemenerji firm is not matching the original and it actually belongs to another construction firm in Australia (hmm.. may be they were also targeted):

Now we know that this mail was likely targeted against the Government firm which specializes in Renewable energy and clean energy concept.
With curiosity I opened the excel file. Yup there blinks the call for enabling macros:

The macro code contained two modules and the below “Workbook_Open()” tells that the VBscript will be executed once the excel sheet is opened.

There were lot of obfuscated codes and random words to confuse static analysis and detection controls to choke.
In the two macro modules , one module was for generation of the encoded code and execution of the decoded commands. The second module acted as the decoding routine for the parent macro module.
The below is the decryption routine for the generated encoded strings.

The below picture shows the variable holding encoded strings and then another variable holding decoded strings :

The main purpose this macro malware was to generate and execute a malicious script , on the fly, by evading the controls and other detection mechanism !

“Word by word” explanation of the above generated code and a video on (on the fly) code generation of the above is described in my article:
https://www.linkedin.com/pulse/time-tiny-video-vbscript-generating-malicious-fly-winston
What would be the malware downloaded by the macro malware?
For finding that, I tried to download the malware from the command and control server,
http://*.*.*.*/~bemkmund/two/files/ji.exe,
unfortunately it failed !!
Part 2 😀
Now lets focus on the Command and control..
The IP belongs to one of the Indonesian Research University and the website contained several vulnerabilities including Directory traversal and File Inclusion vulnerability, which attacker might have exploited, to use it as command and control server.

In quick glance, over these files, we can confirm that the threat should be a spyware and the same server being used as command and control. Running through each of the directories, and found that executable which the macro malware tried to download was not available “ji.exe” , and that’s why it was a failure earlier.
But , ya , I found another executable “wer.exe” !!

Immediately I downloaded, zipped and password protected. (Good to have this habit 🙂 )
It was like getting a cold 1 Litre water bottle while roaming around the desert!
Humans are always greedy, I kept that 1 Litre bottle safe and again roamed to the north side of desert, if I can get some more water bottles :p
After a long walk, volaa!!!! I found a “tunnel” instead of water bottles which echoed river on the other side.
Its wso shell! Now I have to run through the tunnel to reach the river 😉

Keeping in mind that I have only “minutes to seconds” to run through it, I tried to grab things quickly.

The same files which we saw earlier, but this time with full privilege to it.
While I was going through the directories and all other areas,
I could see there were plenty of campaigns happening from this server. From Targeted phishing for Banking sectors, Government sectors, Educational sectors, Health Sectors and much more. I would share details regarding these phishing campaigns later in another article
As of now I am concentrating on the threat we are discussing,
While I was digging more with the URL, I could see a password prompt which I suspected would lead to somewhere special. I was curious about that and tried to get the required info from the shell, if possible .

I began to check each corner to find the password . On the way found full details regarding the database for the WordPress. But didn’t get in, I am not a bad boy.

Again searching through the wilderness I found another piece of script which is a php mailer:

The Php mailer script is “leaf mailer” and we can suspect that this would be used by offender to send bulk spam mails :

My focus was to find the password for the earlier mentioned prompt. One of the config.php got into my eyes and I saw a hardcoded password. From adjacent codes, it smelled some fishy interface of something !
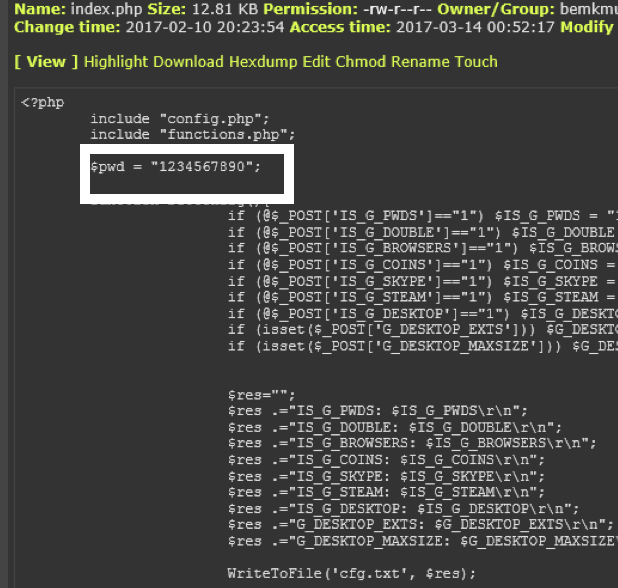
I used this password in the prompt.
Booom !!! It logged in!!
And as suspected, it was the interface of a Spyware “AzorUlt” where all the stolen data of victims populates.

Did a quick research regarding this spyware in Internet:
Proofpoint reported on July 2016 about this spyware in the wild.
https://www.proofpoint.com/us/threat-insight/post/threat-actors-using-legitimate-paypal-accounts-to-distribute-chthonic-banking-trojan
According to Symantec this spyware has been found around July 2016 and below is the technical details from Symantec:
https://www.symantec.com/security_response/earthlink_writeup.jsp?docid=2016-072914-2700-99
The capabilities of this Infostealer:
This Trojan gathers the following information from the compromised computer:
• Bitcoin wallet information
• Steam SSFN file
• Skype main.db file
• Browser cookies
• Autocomplete data
• list of process
• List of installed applications
• User name
• Host name
• Operating system version
• Total RAM
• Application Data directory
The Trojan also gathers files found in the following location:
• %SystemDrive%\Documents and Settings\All Users\Desktop
The Trojan gathers user credentials saved in the following applications:
• Google Chrome
• Yandex Browser
• Comodo Dragon
• Amigo
• Orbitum
• Bromium
• Chromium
• Opera
• Filezilla
• Outlook
• Thunderbird
• Psi
• Purple
Part 3 – The Twist 😮
I believed “AzorUlt” was the spyware or one of the module of “wer.exe” which I plucked from the C&C.
Embarassingly !! there was no relation between “wer.exe” and Spyware “AzorUlt” which we just now found.
Hmm.. So our Malware is something else !
Let me break the twist !
I analyzed the malware “wer.exe” and shockingly it revealed that it is the brand new variant of an infamous spyware “Agent Tesla”.
This malware executable creates a process with name “wer.exe” and immediately spawns a child process with same name. This process will have “high” integrity as well. Some mechanism is obviously acquiring the high integrity, we have seen these spywares comes with inbuilt UAC bypassing skills.

The child process properties:

Then this malware will try to connect to checkip.dyndns.com


The output we get:

Before I move further let me tell you..
This malware is highly evasive to all the VM, Sandbox, Debuggers, other monitoring tools etc. Obviously, I did a tweak with malware to make it blind, to these tools.
A small example is, malware calling “GetTickCount” Api Call to detect whether it is being debugged or not :

Ok Now we will check what malware is doing after getting the victim current IP address
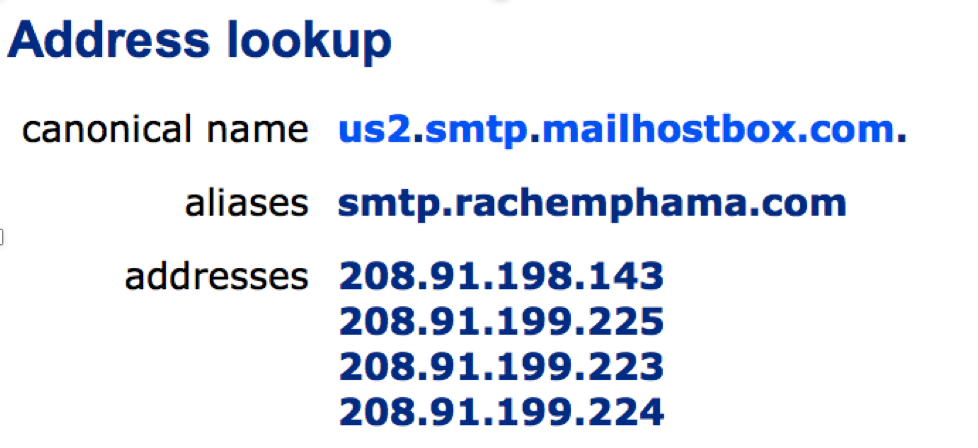
Immediately after IP check, it will try to resolve “smtp.rachemphama.com” which is alias of the CNAME “us2.smtp.mailhostbox.com” which is at IP address “208.91.199.223”

This can be verified by manually doing a telnet to suspected server.

Next the malware is trying to authenticate with “base64encoded login user and password strings”:

Now that we got credentials for the smtp server authentication, we can try manually as earlier:

It works 😉
Now this was the twist which I mentioned earlier :

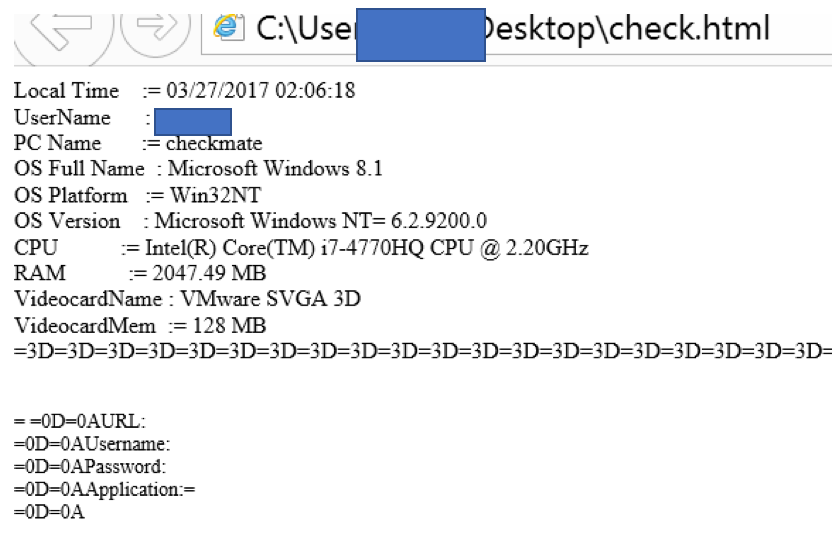
We can see the subject of mail to offender with details(Username/Machine name , IP address) lured from victim machine confirms the malware which we use is “Agent Tesla”
The [Agent Tesla] in the subject of the ex-filtrated Mail subject shows that the hacker is doing a major campaign with lot of other spyware tools, Where SMTP server is same and email ID also same. So this will help hacker to understand the results are indeed from a particular tool. (Each tool serves each Geographical Area)
Now we will see, what data this malware is leaking :

This html message contains below details 🙁
Now that we found that the malware is Agent Tesla, new variant,
I thought of finding the Agent Tesla interface or any other details from the command and control server through “WSOShell”. Throughout my search, I found some image files and other details which is related to Agent Tesla like this:
I did a reverse picture lookup with Google and google gave me results about this picture in relation with “Agent Tesla”

Also we can see the underground hack groups selling this tools across the internet as well.
“digitrustgroup” have mentioned about Agent Tesla early this year:

Nowadays these hack tools are being sold very casually and easily across internet, even this spyware have dedicated website for selling and 24/7 support!!

Now this threat is revamped and might have started spreading with new features across internet.
As we saw, further analysis confirmed that the malware we analysed is “Agent Tesla” which is brand new variant is not yet reported as of now , anywhere . Also no Antivrus have signatures for this malware.
Easter Eggs 😛
In Real Time, I saw hacker uploaded two other malware in the same folder after some hours:

Before I could get hold of those too, my access was lost due to some reasons.
One reason can be hacker understood and kicked me out, or another reason can be some other researchers found and seized , or even university cleared the security holes. Anyways, I got atleast some time to run around the hackers arena and his activities for while.
In our malware specimen, exact capabilities of Agent Tesla, as described in the Hacker underground forums and website was identified:
The capabilities are so huge and encloses all the dimensions of spying activity couple of them are given below:
Agent tesla module for webcam screenshots and screen captures. As the website claims they now have “imgur” as their image server, we can see the traces of this:


All the capabilities of this spyware was found and it is not feasible to list it down one by one. In one word this malware is harvesting every drop of information from the victim machines.
In several underground forums this tool is freely available:

The full capability of this threat is below, “module by module”:
Oh Ya , all these features were absolutely present in the sample as well !!
Features
[+] %100 Fully Undetectable (FUD)
[+] .NET 2.0
[+] server~200kb
[+] Auto Update
[+] Save Options
[+] SMTP
[+] HTML Log
[+] Keyboard Hook (All characters)
[+] Clipboard Hook
[+] On-screen Keyboard Hook
[+] Screenshot
[Assembly]
[+] Assembly Changer
[+] Assembly Cloner
[+] Icon Changer
[stealer]
[+] Chrome
[+] IExplorer
[+] Firefox
[+] Opera
[+] FileZilla
[+] IMVU
[+] Pidgin
[+] FlashFXP
[+] SmartFTP
[+] CoreFTP
[+] FTPCom
[+] NO-IP
[+] Paltalk
[+] DynDNS
[+] Yahoo
[+] MSN
[+] Steam
[+] JDownloader
[File Binder]
[+] Multi File Binder
[+] All Extension
[+] “Just one time” Option
[installation]
[+] Injection (RunPE)
[+] Add Startup (hide from msconfig) (Bypass UAC)
[+] Hide File
[+] Persistance
[+] Melt File
[+] Delay Execution
[+] Kill Process
[Options]
[+] Block Anti-Viruses
[+] Protected Process (Bypass UAC)
[+] Block Rightclick (Bypass UAC)
[+] Kill Taskmanager
[+] Kill CMD
[+] Kill Regedit
[+] Kill System Restore
[+] Disable Taskmanager
[+] Disable CMD
[+] Disable Run
[+] Disable Registry
[+] Disable System Restore
[+] Disable Control Panel
[+] Disable MSConfig
[+] Disable Folder Options
[+] Downloader
[+] File Pumper
[+] Extension Spoofer
[Fake Message]
[+] Header
[+] Message
[+] Style
[+] Button
[Web Options]
[+] Host Edit
[+] Web Filter (Bypass UAC)
[+] Add UAC Manifest
The agent Tesla interface will be like this:

IOC
MD5
4CDC4F2C1849371E015A39A9D4103E87
68AB498574C0BEAE225A04D04A2571A1
URL
smtp.rachemphama.org
us2.smtp.mailhostbox.com
checkup.dyndns.org
IP
208.91.198.143
208.91.199.225
208.91.199.223
208.91.199.224
Conclusion
It was of course a fantastic journey from the spam mail till the Offenders command and control server resources. One thing I understood when gliding through the Command and control of the attacker is that , It is dangerous, if we are not giving enough seriousness for Cyber security. Like UTM devices, now a days malware have multiple capabilities and architecture to successfully evade any security controls and infecting the end machine.
When peeked into the hackers arena, I could see numerous malicious scripts, targeted phishing links, Industry specific attack strategies, Spyware, Trojans, Ransomware, PHP shells so on and so forth. If one command and control server contained these many attack vectors means, globally it is not at all imaginable .. It is way outside the Ball park !
Like “Agent Tesla” Spyware several others are getting revamped and cooked inside. How effective are our security controls to defend against these threats. If you ask me, I would say, we are no where ! Lets hope one day we can say we are indeed capable to detect and defend these threats.
References
https://www.symantec.com/security_response/earthlink_writeup.jsp?docid=2016-072914-2700-99
https://www.linkedin.com/pulse/time-tiny-video-vbscript-generating-malicious-fly-winston
This is by far the best analysis and conclusion, I have seen in the net. You have become a master now. Hats off.
Thanks Amit 🙂
Winston, I just love the way you do your analysis – easy to follow.
Just as you mentioned how effective our security controls are to defend these threats, “we are no where”.
Thank you so much Obum. I am happy that you liked my article .. 🙂
Awsome analysis and explainations , the best i have ever seen
thanks man
Nicely articulated. Simple & easily understandable writing.
Great JOB. KEEP ROCKING.
Thank you for sharing.
Sir,You explain very well. Appreciable
Excellent Analysis .The way you started and end your analysis .It’s awesome.It’s like a Champ!!!
Too good…. Congratulations and very all the best…
Great analysis Winston, thanks for the detailed breakdown.